Shadow IT: The Vendor Risk You Can't See
78% of organizations have unknown SaaS applications in their environment. Discover how to identify and manage shadow IT before it becomes a breach.
Blog
Expert perspectives on third-party risk management, evidence validation, and the operational shift from static reviews to continuous vendor defense.

Featured Article
Annual questionnaires create a false sense of security. Learn why point-in-time assessments fail to capture real vendor risk and what to do instead.
78% of organizations have unknown SaaS applications in their environment. Discover how to identify and manage shadow IT before it becomes a breach.
The future of third-party risk management is continuous monitoring. See how leading enterprises are shifting from reactive to proactive vendor oversight.

Struggling to get budget approval? Use our ROI framework to demonstrate the cost savings and risk reduction of automated TPRM.

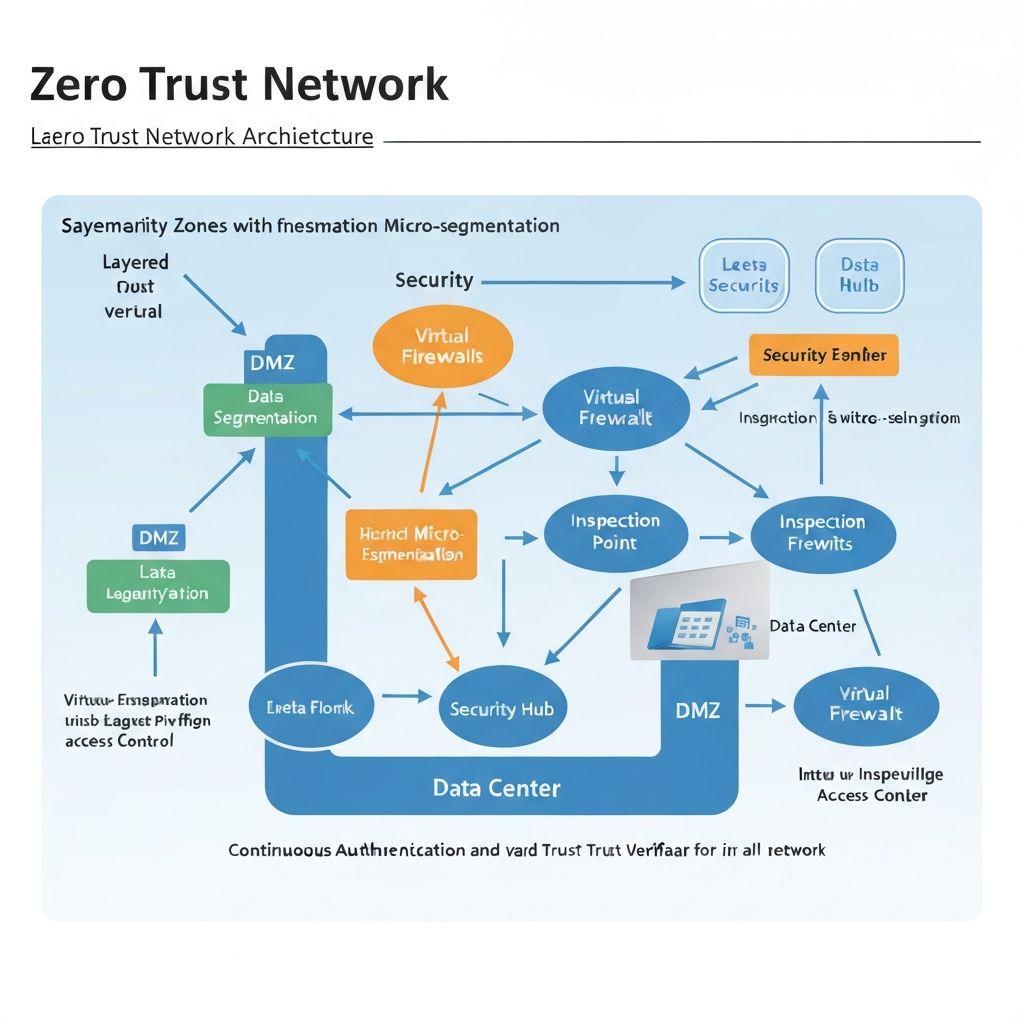
Security Architecture
Zero trust isn't just for employees. Learn how to extend never trust, always verify principles to your vendor ecosystem.

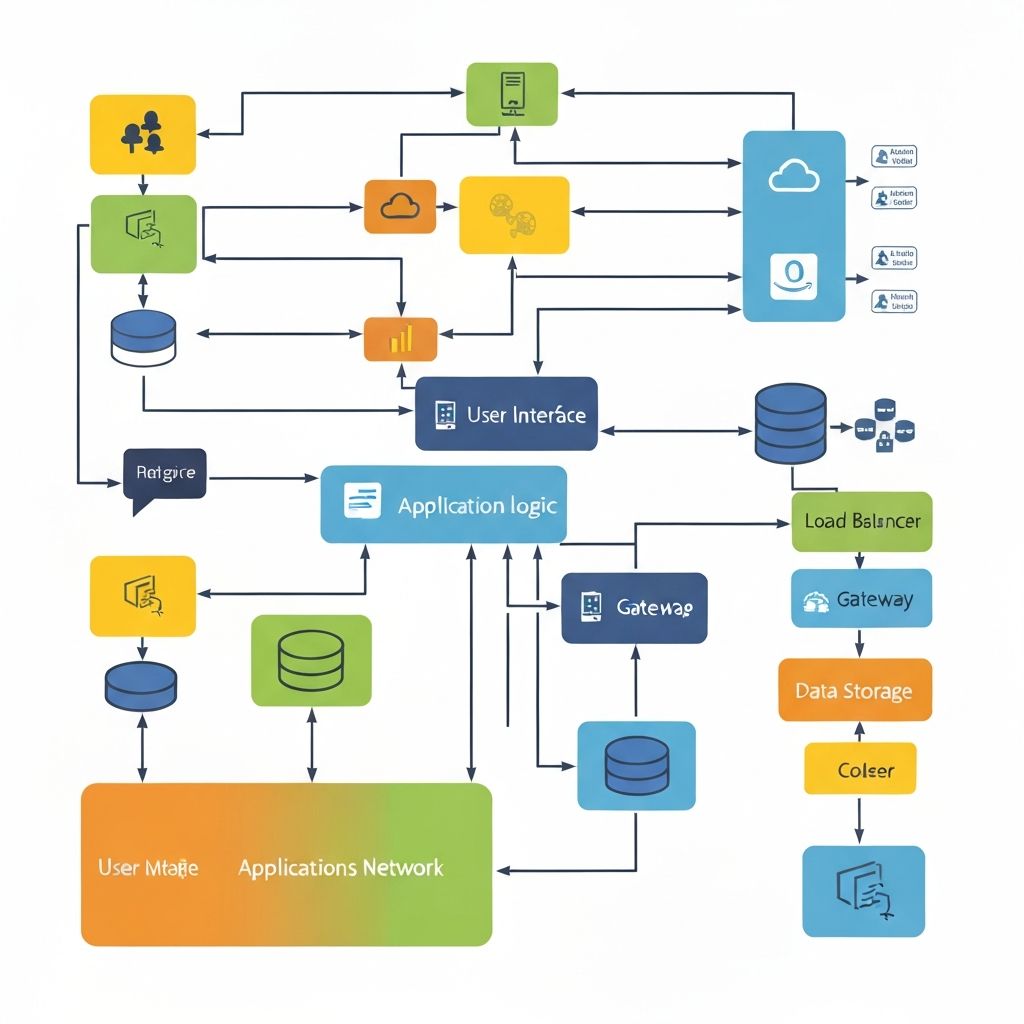
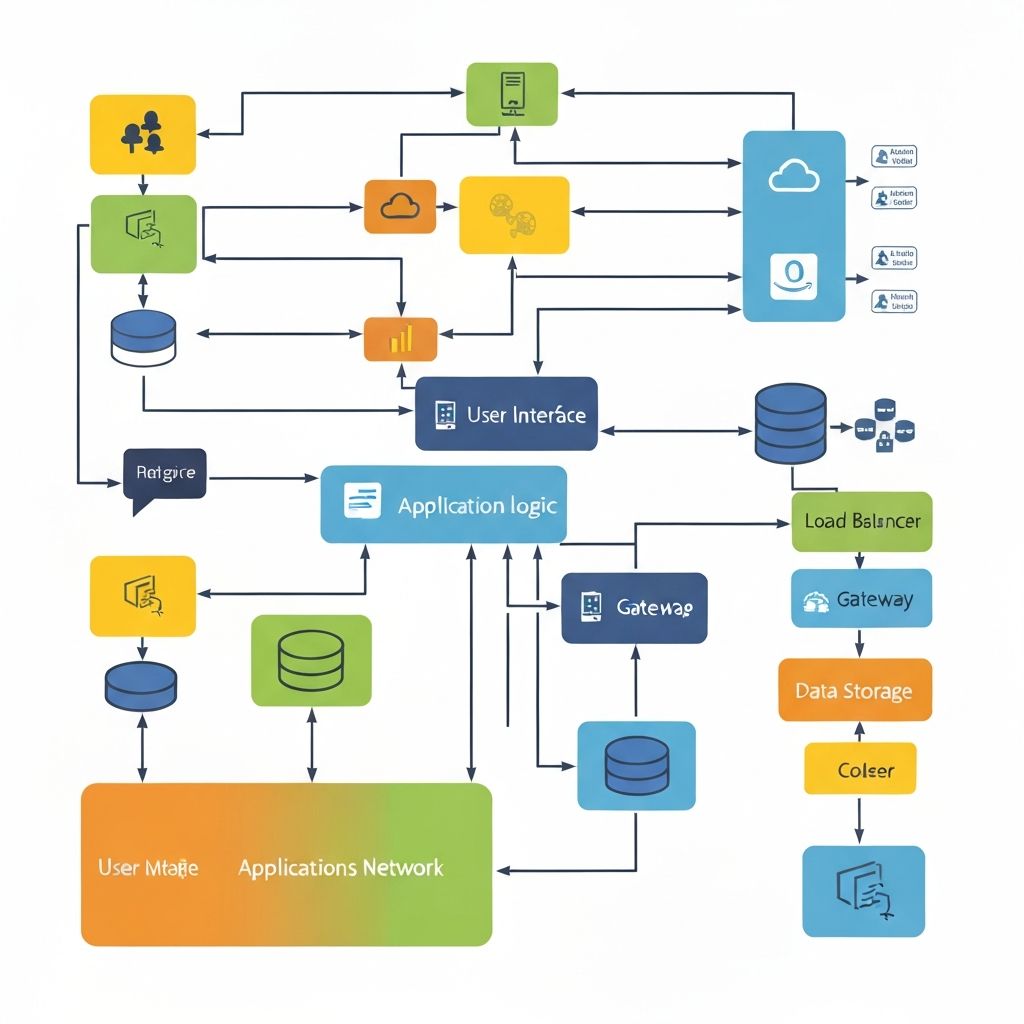
Technology
Artificial intelligence is revolutionizing TPRM. Explore practical applications that are delivering results today—not science fiction.
Newsletter
Get practical guidance on vendor assessments, evidence validation, and continuous monitoring delivered to your inbox.